Cybersecurity is an issue that all businesses, regardless of size, must address. Cyber threats are evolving, and they can be devastating to a company’s reputation, bottom line, and even existence. In this blog, we will discuss the four essential steps to protecting your business from cyber-attacks.
4 Steps to Protect your Business
Step 1: Have a plan
The first step to protecting your business from cyber-attacks is to have a plan in place. This plan should outline the steps your company will take to prevent and respond to cyber-attacks. It should also define roles and responsibilities for all employees, including who will be responsible for responding to security incidents.
If you’re not sure where to start, you can download a free copy of the Critical Security Controls from Center for Internet Security. This download is broken down into 3 implementation groups which allows you to choose the tier most applicable for your business.
Step 2: Build resilience – start with the fundamental security tools
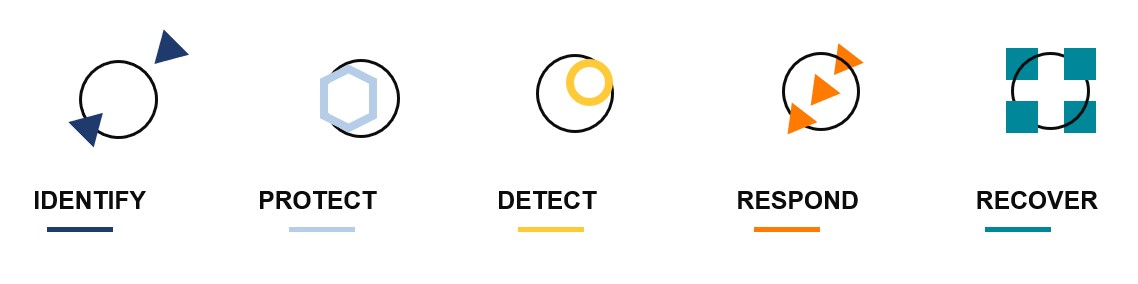
Source: NIST/Cyber Framework
The second step to protecting your business from cyber-attacks is to build resilience by starting with security tool fundamentals. This includes tools such as Managed Detection and Response (MDR), E-mail threat detection, Multi-Factor Authentication (MFA), & more.
These security tools can help you detect and prevent cyber-attacks. They can also provide you with valuable information about the types of threats your business is facing, allowing you to take proactive measures to protect your company’s assets.
Step 3: Inventory your IT assets
The third step to protecting your business from cyber-attacks is to inventory your IT assets before the threat actors do. This involves identifying all the hardware and software in your network and determining their level of security.
By conducting an inventory of your IT assets, you can identify potential vulnerabilities and take steps to secure them. You can also ensure that all software and hardware are up to date with the latest security patches.
Step 4: Create Incident Response Plan
The final step to protecting your business from cyber-attacks is to think through and put an initial incident response plan in place. This plan should outline the steps your business will take in the event of a security incident, including how to contain the incident, how to recover from it, and how to communicate with stakeholders.
Your incident response plan should also include:
- Incident response team: Identify the members of your incident response team and their roles and responsibilities.
- Communication plan: Develop a communication plan that outlines how you will communicate with stakeholders, including customers, employees, and regulatory bodies.
- Testing and training: Test your incident response plan regularly to ensure that it is effective. Provide training to your employees to ensure that they know how to respond to a security incident.
Protecting your business from cyber-attacks is not a one-time task. It requires ongoing effort and attention to detail. By following these four essential steps, you can help secure your business’s assets and reduce the risk of a cyber-attack. Remember, prevention is always better than cure, and it is much easier and cost-effective to prevent a cyber-attack than to recover from one.
Watch the full webinar
Learn about today’s threats, how to effectively manage your cyber risk, and 4 steps you can take today to prepare your business from what’s coming next: 2023 State of Cybersecurity | You Will Be Breached







