With cyber threats evolving constantly, it is essential for everyone to be well-versed in security awareness. The global cost of cybercrime in 2022 was $8.44 trillion and it is estimated to jump to $23.84 trillion in 2027. Source: Statista Cybersecurity Report Whether you’re a student, a professional, or simply someone who uses the internet, understanding these four crucial security concepts will empower you to protect yourself and your sensitive information from potential threats.
4 Critical Security Awareness Concepts
1. How to Recognize a Phishing Email
- Unknown sender, or known sender contacting you a new way
- Poor grammar and spelling
- You’re being asked to provide protected information
- Strange links or unexpected attachments in the email
- Sense of urgency – you must react now
Here’s examples of real phishing attacks so you can better understand how to recognize when you’re under attack.
Example 1 of a Mass Phishing Email:
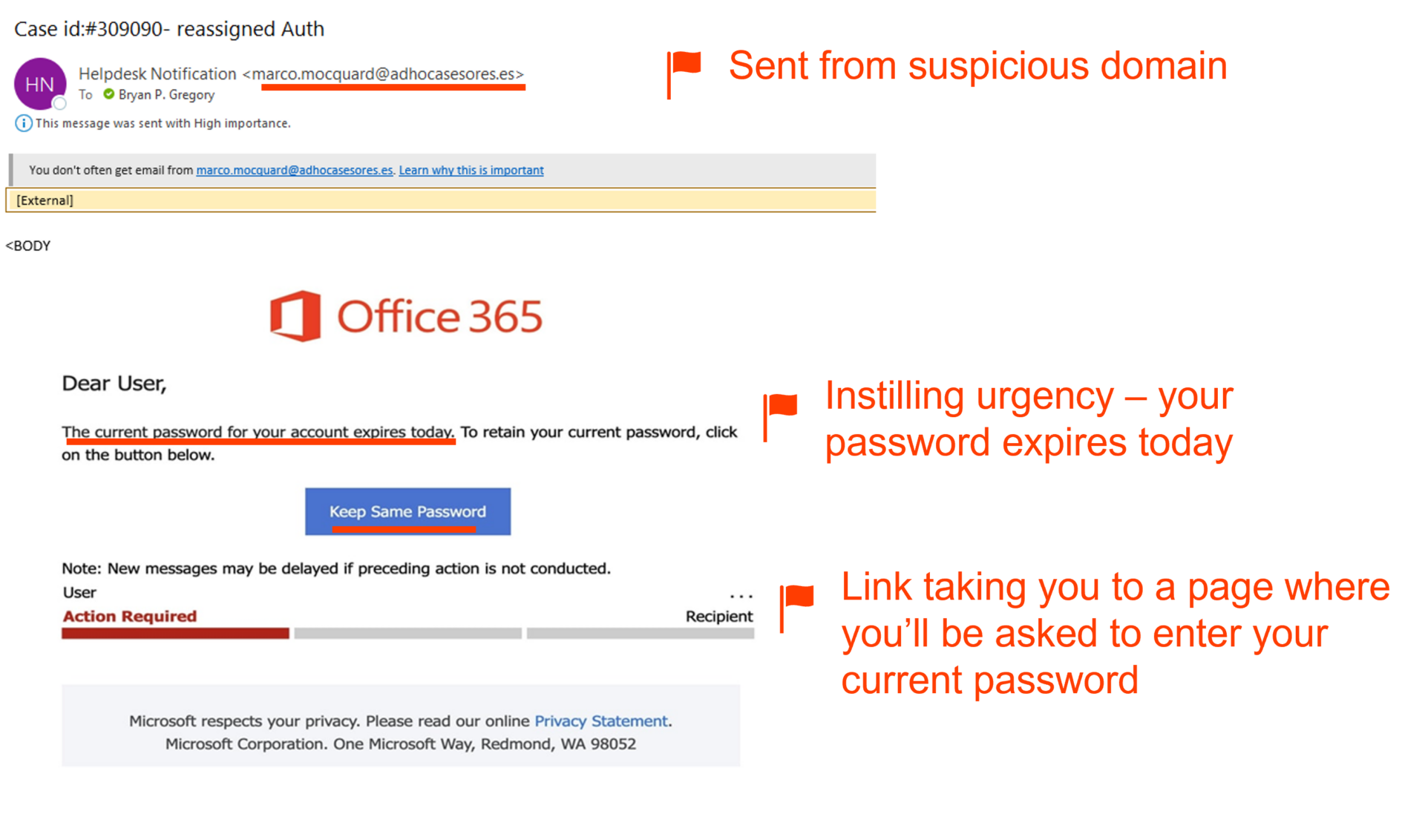
Example 2 of a Mass Phishing Email:

Example of a Spear Phishing Email:

Source: Tessian
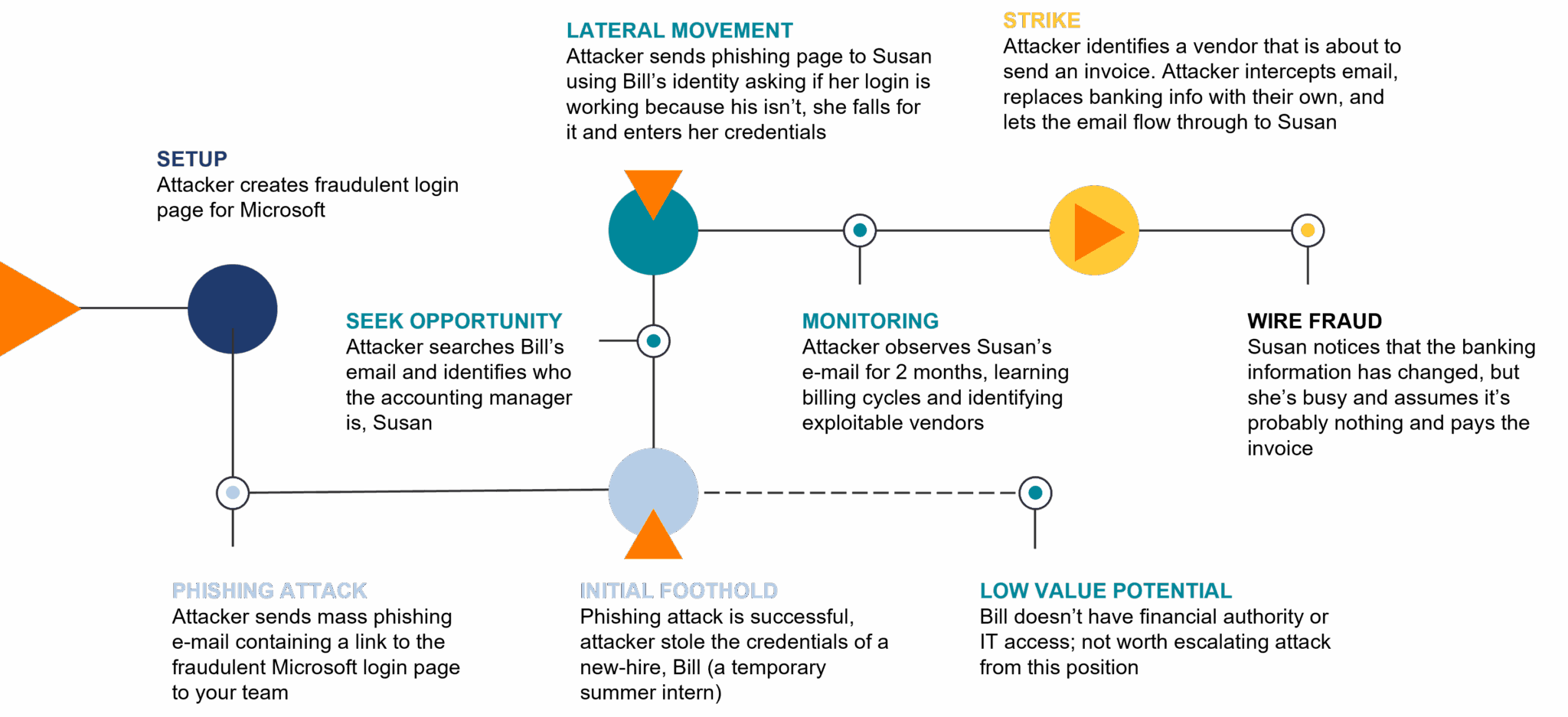
2. How an Email Compromise Works
An email compromise is a sophisticated cyberattack that targets individuals, businesses, or organizations.
- The process typically begins with the cybercriminal conducting thorough scouting, gathering information about the target.
- With this intelligence, they craft convincing phishing emails tailored to the target’s interests and habits, often impersonating a trusted contact, executive, or service provider. The email might contain urgent requests for sensitive information, financial transactions, or credentials.
- Email compromise can lead to severe consequences, including financial losses, data breaches, and reputational damage.
Here’s an example:
3. How to Report Phishing Attacks the Right Way
When to get help:
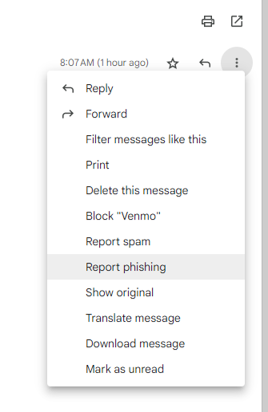
When you receive a phishing email, use the Report Phishing button or let your IT Team know.
Outlook:

Gmail:
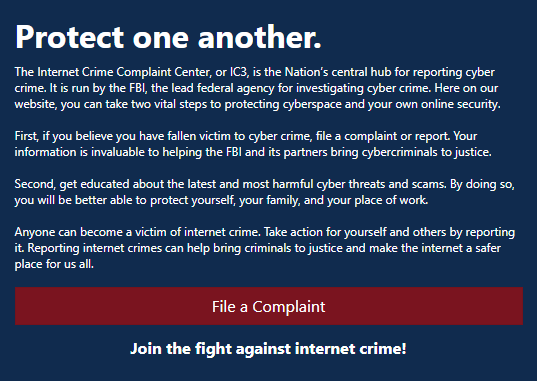
If you think you’ve been compromised, report it immediately! To ensure a swift and effective response to any successful cyberattacks, you can go to the FBI’s Internet Crime Complaint Center (IC3). The IC3 serves as a vital hub for reporting and documenting internet-related crimes, including cyberattacks and online fraud. By utilizing this platform, you can play a critical role in assisting law enforcement in their efforts to combat cybercrime and protect both individuals and businesses from digital threats.
When you are uncertain, STAY CAUTIOUS and call a trusted person or your IT team.
4. Understand Basic “Security Hygiene”
- Don’t use your company login credentials on 3rd party websites, they could have a data breach and expose your credentials to the world.
- Be vigilant every single time you’re asked to share protected information or make a financial decision, no matter who you’re talking to
- Don’t install “grayware” on company devices, and don’t work from devices that your kids use.
- When working from a personal device…
- Don’t save protected information (work logins, client data, etc.) on the device itself.
- Use the web versions of your tools whenever possible.
- Call to verify when…
- You get updated banking information.
- Asked to do something unusual, urgently.
- You receive an email that your account has been compromised.
- If someone is demanding information from you, don’t call the number listed in email, or reply directly – search for it online or ask a colleague.
Security awareness isn’t just an option—it’s like trying to function without coffee, an absolute MUST! As our lives become increasingly intertwined with technology, the risks of cyber threats continue to grow exponentially. By grasping these five crucial security awareness concepts, individuals can fortify their defenses, safeguard their sensitive information, and contribute to a safer cyber landscape for everyone.
Watch the Full Webinar
Discover the latest insights, best practices, and proactive measures that can safeguard you and your organization from potential threats. Watch our full Security Awareness 101 webinar now and take your security awareness to new heights with guidance from our seasoned professionals.
Don’t Take the Bait | Are YOU Smarter than a Phisher?
Play this phishing game and see if you can outsmart the scammers!







