Today’s business must learn how to operate in an increasingly hostile digital landscape – it is not a matter of if, but when you will get breached. We recently investigated a cyberattack that illustrates the importance of network visibility and what happens when you’re unprepared for an attack.
[Security Insight] Addressing Cybersecurity Breaches and the Vital Role of IT Governance
The Initial Compromise
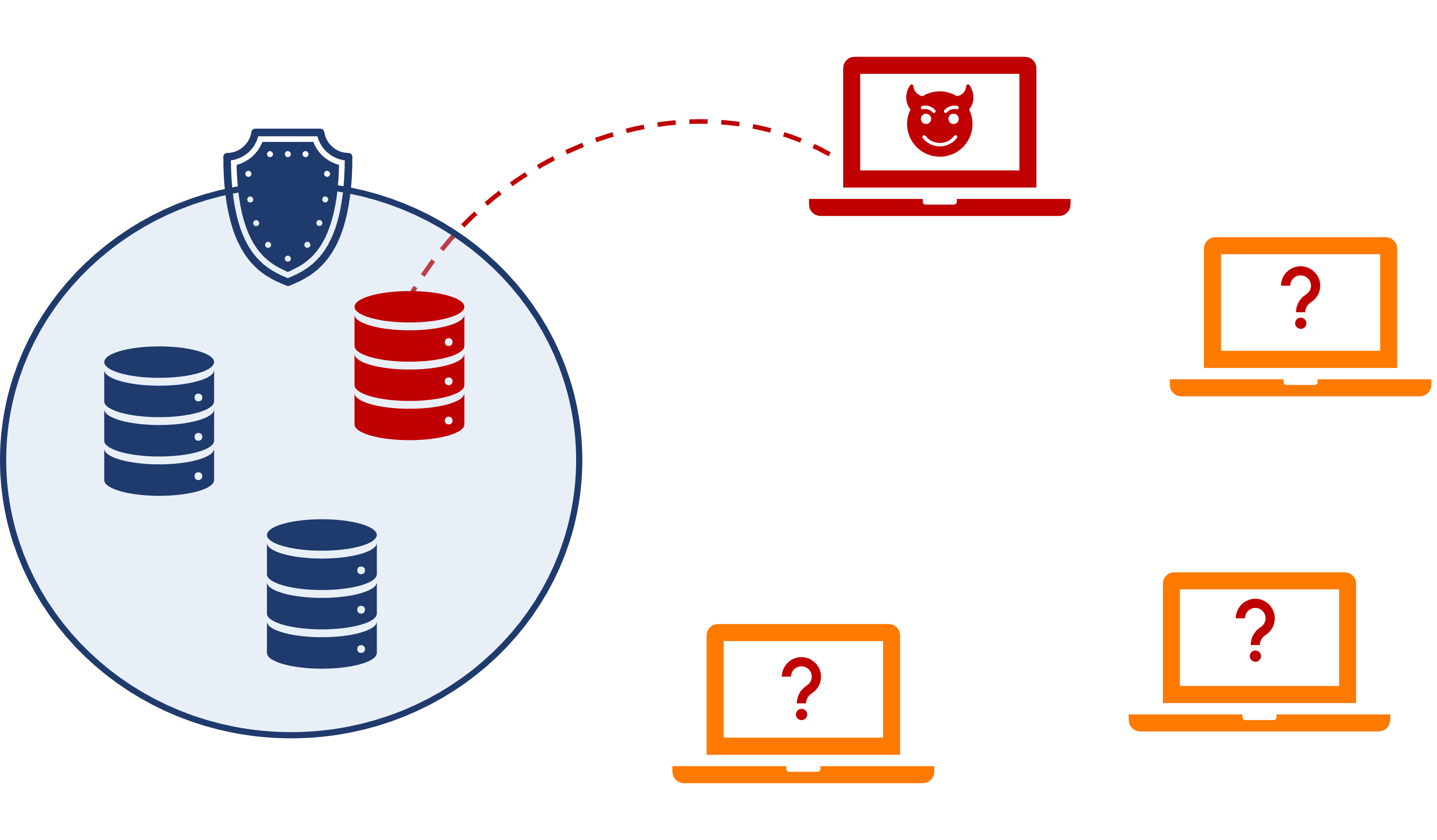
Unfortunately, the victim was working from a device that wasn’t managed by their company’s IT team. This means there was no way to identify the source of the original compromise – how or when the threat actor breached the device.
The firm had a “bring your own device” (BYOD) policy in place, allowing employees to use their personal machines for work purposes. While this policy offered flexibility, it also introduced a significant risk factor. The compromised user’s machine was not owned by the firm, but it was connected to the firm’s network through a VPN, giving the threat actor access to the firm’s network.
The Escalation
Once inside the network, the threat actor wasted no time and began enumerating IT information about the firm’s user accounts. The threat actor began to expand their attack to other servers, presumably searching for more valuable data to steal or technical vulnerabilities to exploit. The firm’s servers were equipped with our required fundamental security tool, Managed Detection & Response (MDR). As soon as the threat actor expanded their attack to a managed device (i.e., their server), alarms went off and notified the security team that something might be wrong.
The Aldridge Security Team’s Response
The security team validated the threat and alerted the network team that a threat actor had compromised the targeted firm’s server. The network team had to isolate the firm’s network, completely stopping the firm’s operations. A full shut-down was necessary because this firm had many unmanaged BYOD workstations connected to their network. The only way for them to be certain that no further damage was taking place, was to stop everyone from doing anything.
After the immediate damage has been stopped, the next goal is to re-establish trust in the victim’s IT. The Aldridge security team re-establishes trust by finding a part of the victim’s IT that was unaffected by the breach, and systematically reviewing the pieces that connect to that system to “expand” the circle of trust. The security team was able to bring systems back online as they determined they were clean.
The Feds Arrive
Days into the Aldridge security team’s investigation, agents from the Department of Homeland Security (DHS) reached out to the firm. DHS had found the firm’s data on the dark web and wanted to inform the victim that they had likely been breached. This was not news to the firm, as they were already well into the investigation and recovery process. The DHS, pleasantly surprised that the firm was already responding to the attack, synced up with our security team to get up-to-speed.
The Outcome
The threat investigation and recovery process took 2 weeks. The investigation phase concluded within three days, while the subsequent two weeks were dedicated to rebuilding trust and restoring the infrastructure. The firm experienced complete downtime during the first phase of the investigation, and disruption for the entire 2 weeks. The threat actor managed to uncover some information about the firm’s users, but nothing that is legally protected like financial information or Personal Identifiable Information (PII).
The victim firm was lucky that the threat actor appeared to be an inexperienced individual (as opposed to an organized group) and triggered security alerts before they were able to do any serious direct damage. However, the investigation and recovery process were particularly painful due to the lack of visibility and confidence in the firm’s IT perimeter.
Lessons Learned
The Basics Aren’t Cutting it Anymore
The firm decided to take a proactive approach to prevent future incidents of this magnitude. They opted to deploy our complete security stack. A key element to our security stack is Security Information & Event Management (SIEM). SIEM provides the security team with far more visibility into the firm’s IT, allowing them to catch more sophisticated threats sooner. SIEM also brings all your security telemetry into one place, making investigations far quicker and certain.
The Importance of IT Governance
Enabling Bring-Your-Own-Device (BYOD) policies and granting access to sensitive company data from entirely unmanaged devices reflects inadequate IT governance. The firm’s decision-makers entrusted the office manager with IT responsibilities, despite their disinterest in the field. Because the firm did not have an IT stakeholder that would be directly affected by a security breach, our security recommendations fell on deaf ears and the firm was not prepared for an attack.
In the aftermath of this breach, the firm acted by appointing an executive to oversee all IT decisions. This decision represents a significant shift towards a more robust IT governance model, ensuring that expert recommendations are heeded, and cybersecurity protocols are enforced.
It Can Happen to You
We’ve seen this time and time again, businesses ignoring security until they are face-to-face with a disaster. It’s understandable, cybersecurity is a relatively new and complicated concept. It’s easy to not invest in something you don’t understand and haven’t experienced. Our goal is to share real stories of businesses that are affected by cybercrime so that you can learn from their experience and take action to prepare your business before it happens to you.
Expand Your IT Perimeter
The victim firm had an extremely tight IT perimeter. They thought the only thing they needed to protect was their servers, because that is where their valuable data lives. After this event, the firm learned the importance of expanding their IT perimeter to include the devices that access their data.
Start Working Towards Better Security
You should not be worried whether you’re secure. Partner with Aldridge and become confident that you’re prepared for whatever happens next. Look at our IT Security page to see how we can help.







