Cybersecurity is no longer just about protecting systems, it’s about protecting people.
Attackers are increasingly targeting executives directly, using their identity, influence, and access as entry points into organizations. These attacks often don’t look like traditional cyber threats, which makes them harder to detect and easier to fall for.
Digital Identity Theft Is on the Rise
One of the fastest-growing threats today is digital identity theft. This is not a system breach, it’s someone impersonating you.
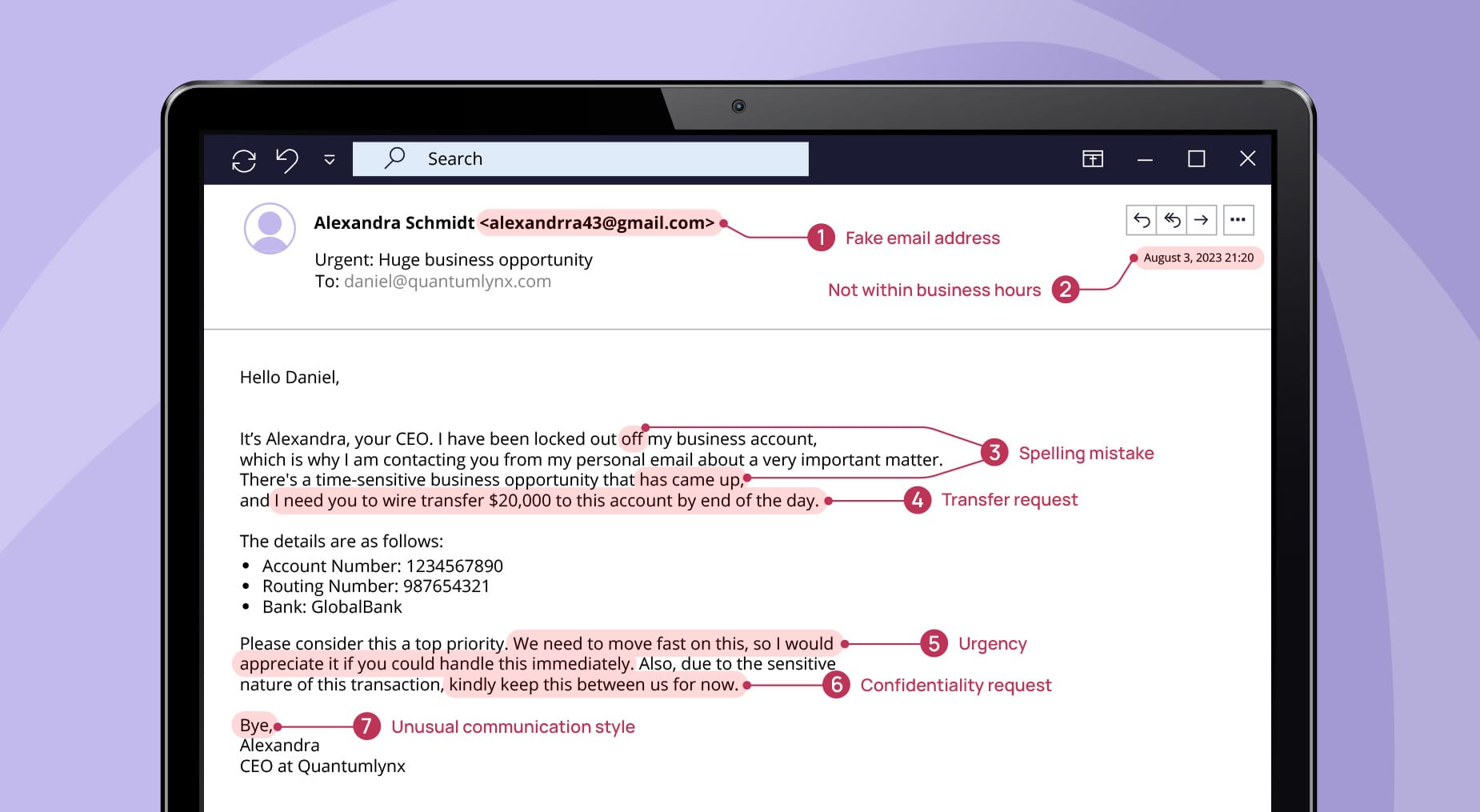
Attackers are taking publicly available information from sources like LinkedIn or company websites and using it to create:
- Fake LinkedIn profiles that mirror real executives
- Lookalike email addresses that are only one character off
- Convincing impersonations of leadership or trusted contacts
Because these messages appear legitimate, especially on mobile devices, they are often trusted without a second look.
Why These Attacks Work
These attacks are effective because they exploit behavior, not just technology.
Most people do not inspect email addresses closely, especially when:
- The message appears to come from a known executive or colleague
- It arrives on a mobile device
- The context feels familiar or urgent
Attackers are also leveraging AI and deepfake technology to enhance these impersonations, making them more believable than ever before.
Social Engineering Is Expanding Beyond the Workplace
Cyber threats are no longer limited to corporate systems. Attackers are now targeting personal lives to create business risk.
Common tactics include:
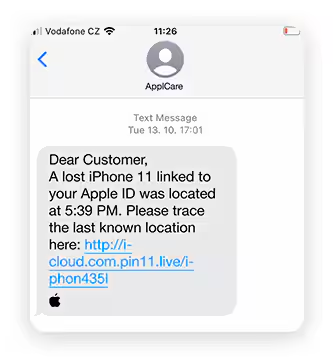
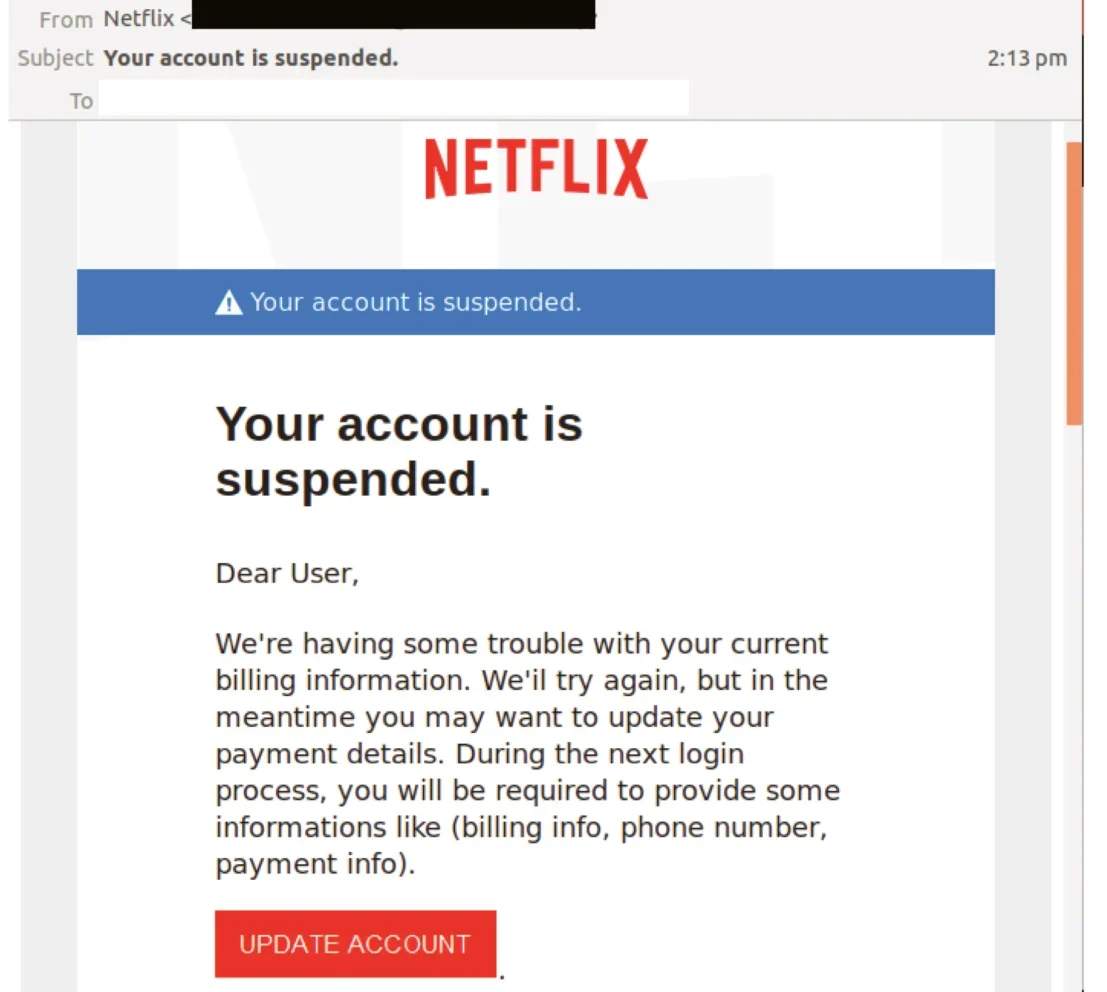
- Spoofed text messages that appear to come from friends or family
- Fake fundraising requests or urgent personal situations
- Messages that use real names, schools, or organizations to build trust
In one example, an executive received what appeared to be a legitimate message from their child’s school requesting support for a teacher. The message was highly detailed and believable, but it was fraudulent and resulted in both financial loss and malware deployment.
Your Home Network Is Part of Your Attack Surface
As work and personal devices continue to overlap, attackers are taking advantage of weaker security controls outside the office.
When a personal device is used for work, a single click on a malicious link, whether from a text message or personal email, can introduce malware into the business environment.
This blurs the line between personal and corporate risk, making home networks and personal behavior part of your organization’s security posture.
Security Layers Are Important, but Not Enough Alone
Many organizations have invested in strong security tools, including:
- Email filtering
- Endpoint Detection and Response (EDR)
- SIEM and monitoring solutions
These layers are essential, but they are not designed to stop every attack. Their role is to:
- Reduce risk
- Detect unusual activity
- Enable faster response and recovery
There is no single control that guarantees complete protection.
Why Incident Response Matters More Than Ever
Because attacks are becoming more targeted and harder to detect, organizations must shift their mindset.
It is no longer just about prevention. It is about being prepared for:
- Detection when something slips through
- Rapid response to contain the threat
- Business continuity during and after an incident
Attackers are well-funded, patient, and increasingly precise in how they operate. They are investing time to ensure their efforts produce results, and organizations need to be equally prepared on the response side.
What Organizations Should Do Now
To address these evolving threats, organizations should focus on both technical controls and human behavior:
- Enforce consistent security controls across all users, including executives
- Strengthen identity verification and reduce reliance on visual trust alone
- Educate employees on modern social engineering tactics, not just traditional phishing
- Secure personal devices that access business systems
- Develop and maintain a clear incident response and recovery plan
Cyber threats are becoming more personal, more targeted, and more convincing.
The organizations most at risk are not necessarily the ones with weak technology, they are the ones that underestimate how attackers exploit trust, identity, and human behavior.
Create Your First Real Plan
If you want to be prepared before an incident happens, download our Security Incident Response template for a clear, practical framework to respond quickly and confidently. Talk to Aldridge today to strengthen your security and ensure you’re ready when it matters most.







